Run agents. Stay in control.
One click to a running OpenClaw agent with skills, channels, and policies ready out of the box. For teams that need enforcement and audit trails, Tropic watches every action against your policies.
We remove the technical barrier.
Other platforms give you one-click hosting. Tropic gives you one-click control.
Defense in depth.
OpenClaw is powerful. tropic.bot makes it safe to expose to the world.
OpenClaw Instance
Running · Singapore
OpenClaw Version
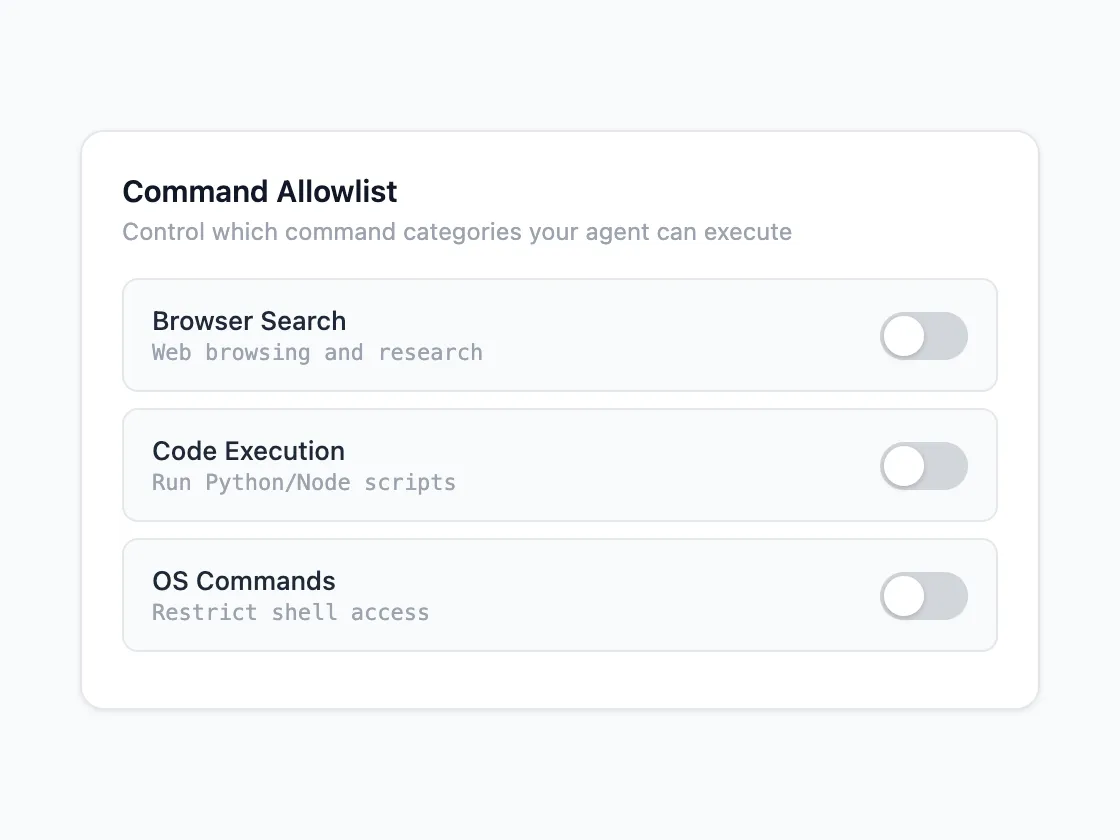
Command Bundles
Toggle what commands each VM can run from the dashboard. Changes apply without restarting the agent.
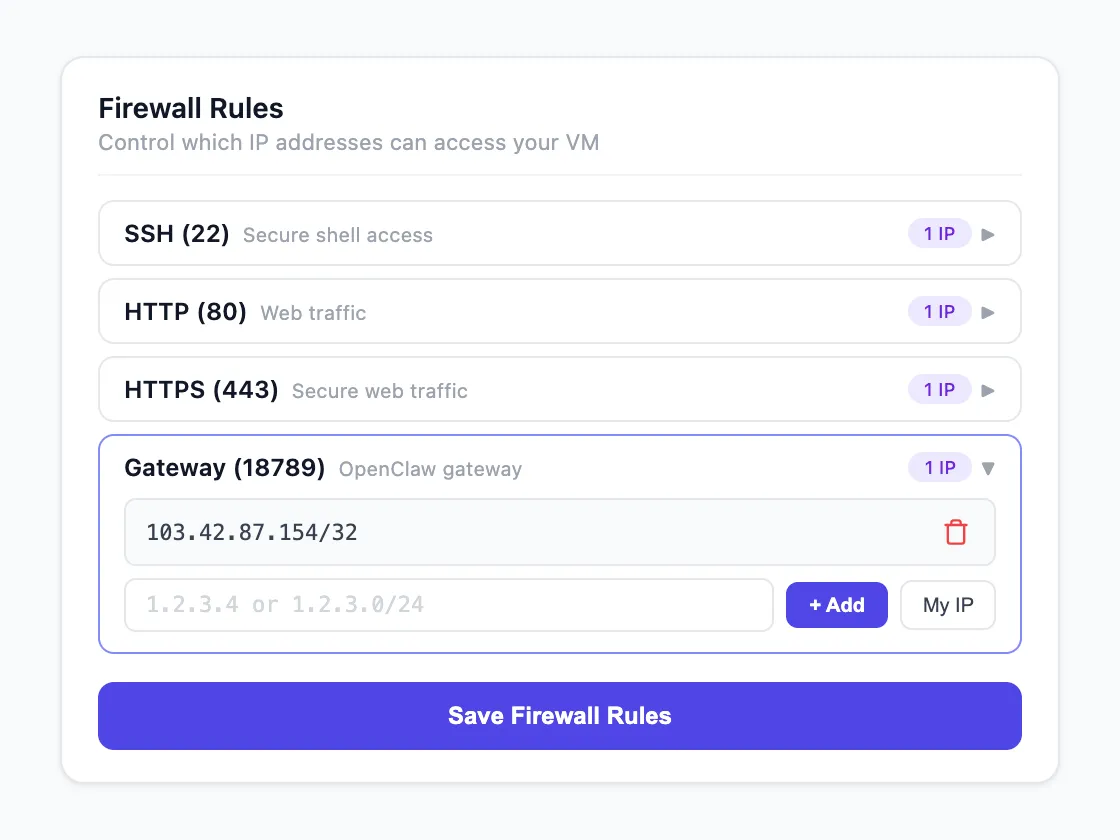
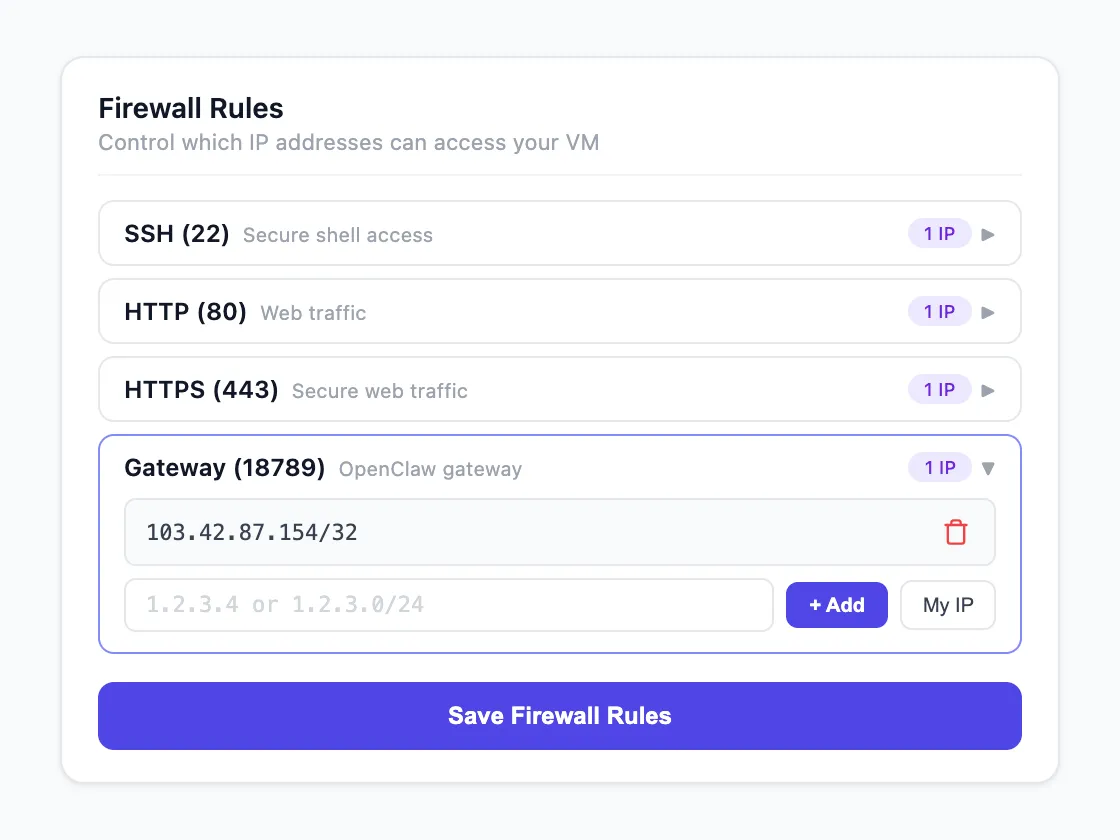
Port Restrictions
Configure inbound port rules from the Tropic dashboard. By default, no ports are exposed to the public internet — traffic goes through Tropic's reverse proxy.
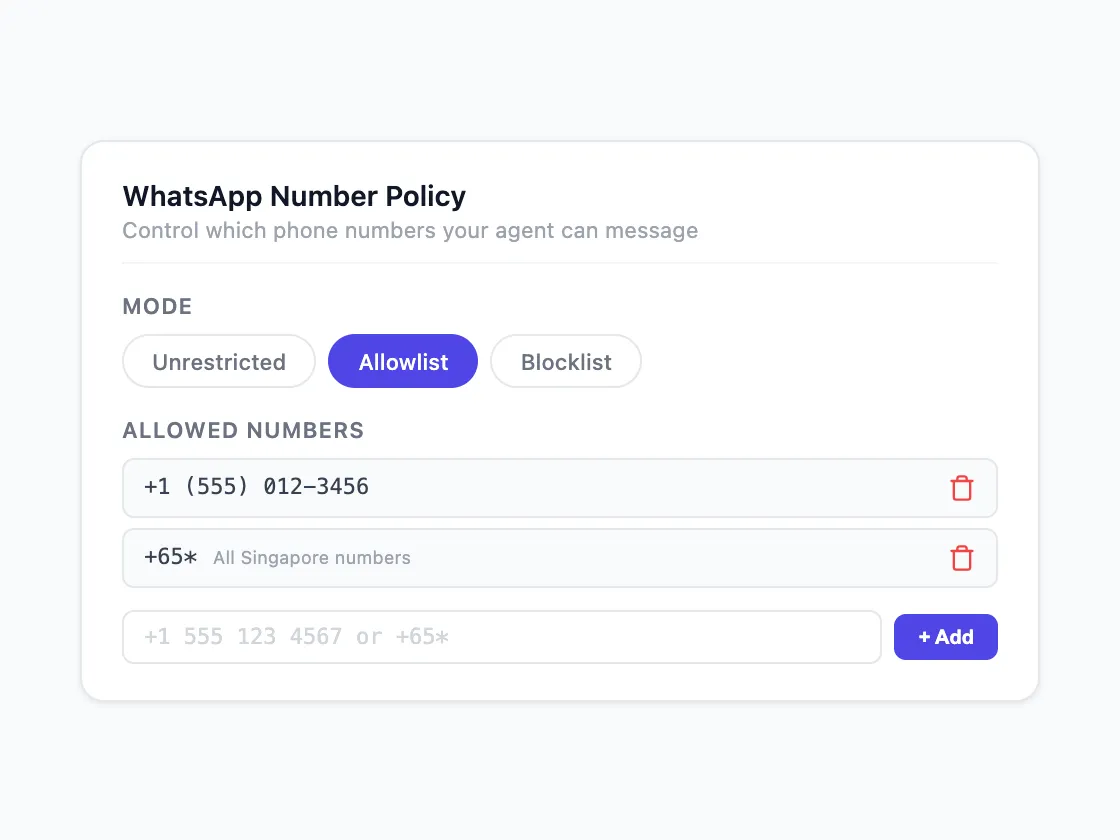
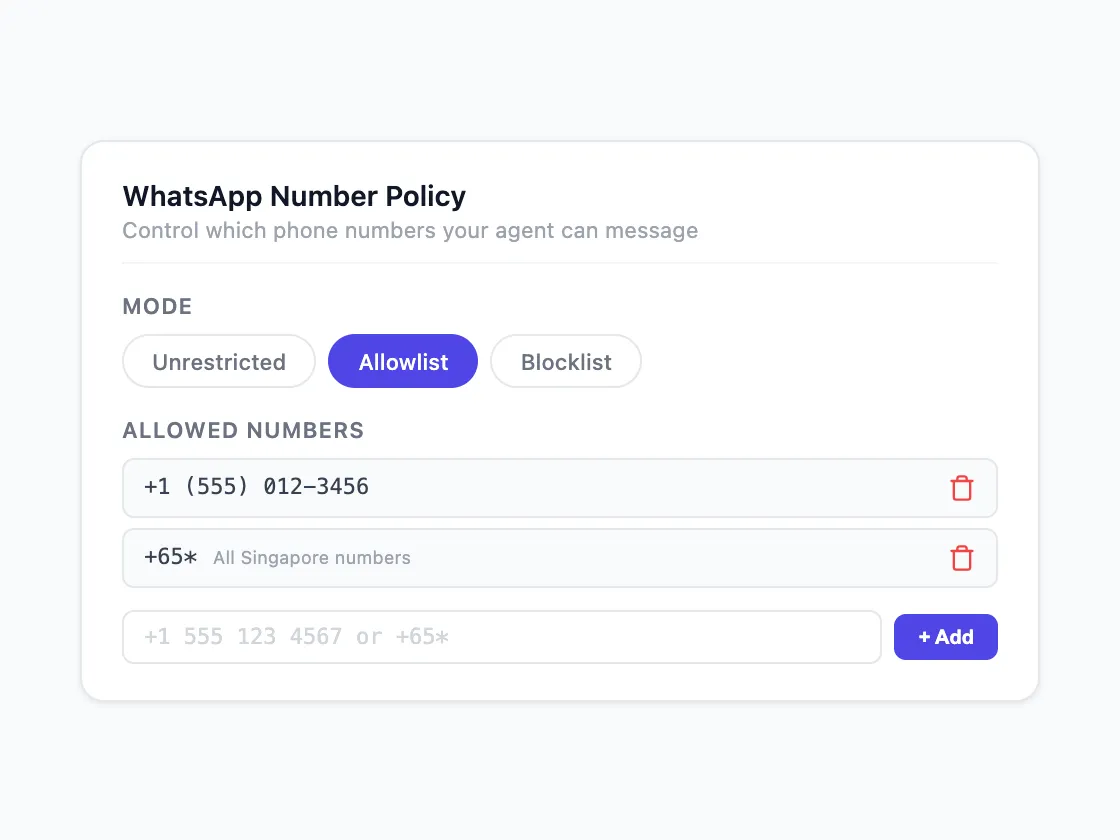
Phone Number Allowlists
Set which numbers your agent can message via WhatsApp. Supports wildcards like +65* for country-level rules. Allowlist, blocklist, or unrestricted.
OpenClaw Instance
Running · Singapore
OpenClaw Version
Always Up-to-Date
We keep OpenClaw patched and hardened. Choose when to upgrade to the latest version from the dashboard.
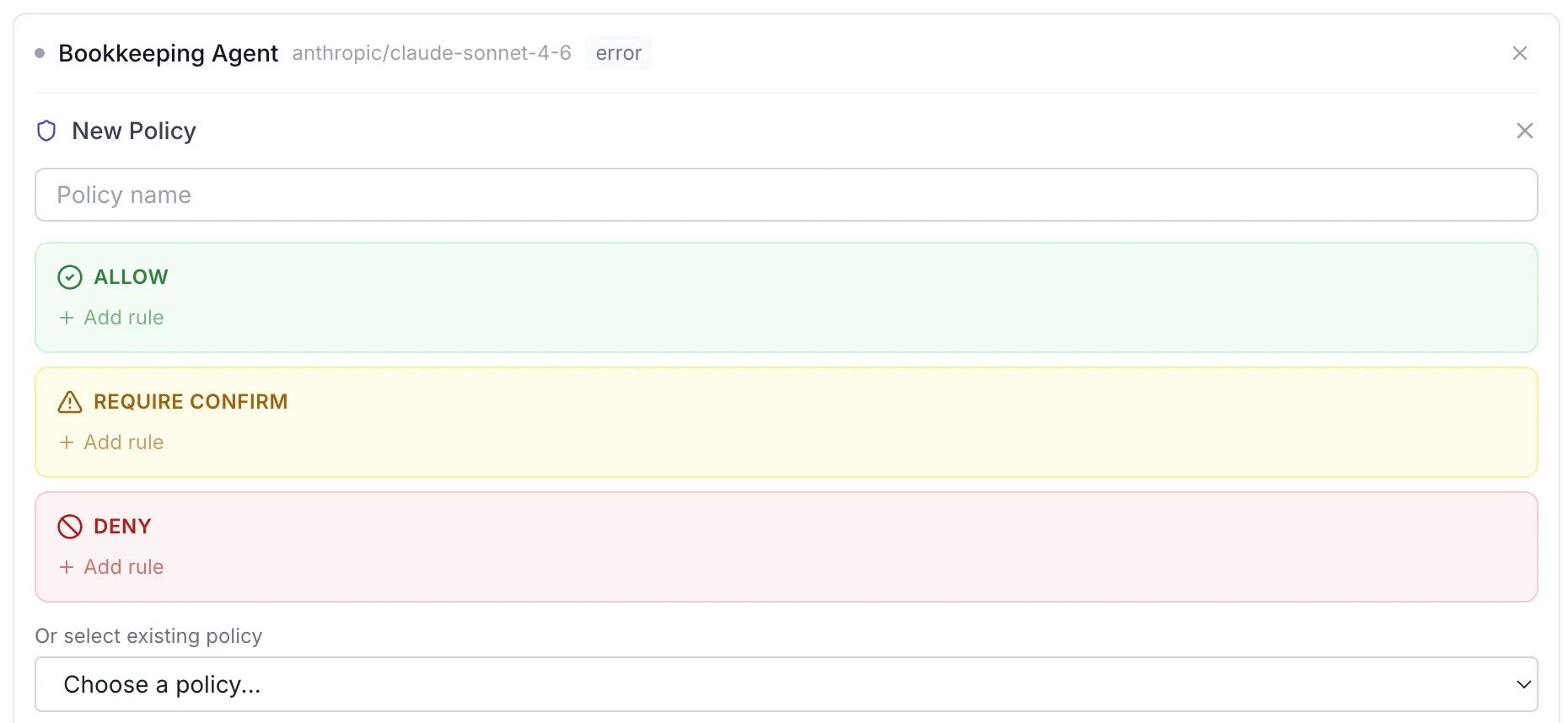
Policies that actually enforce.
Define what your agent can do: Allow, Require Confirm, or Deny. Applied before every action as a hard check outside the model, not as a suggestion to it.
Enforcement runs deterministic rules first. Anything ambiguous goes through a multi-model cross-check: two or more LLMs from different providers independently verify the action against your policy before it executes.
A single model can be manipulated. Cross-checking across independent models with different architectures raises the bar significantly.
This is an active research area. We keep iterating as new techniques emerge. See our roadmap.
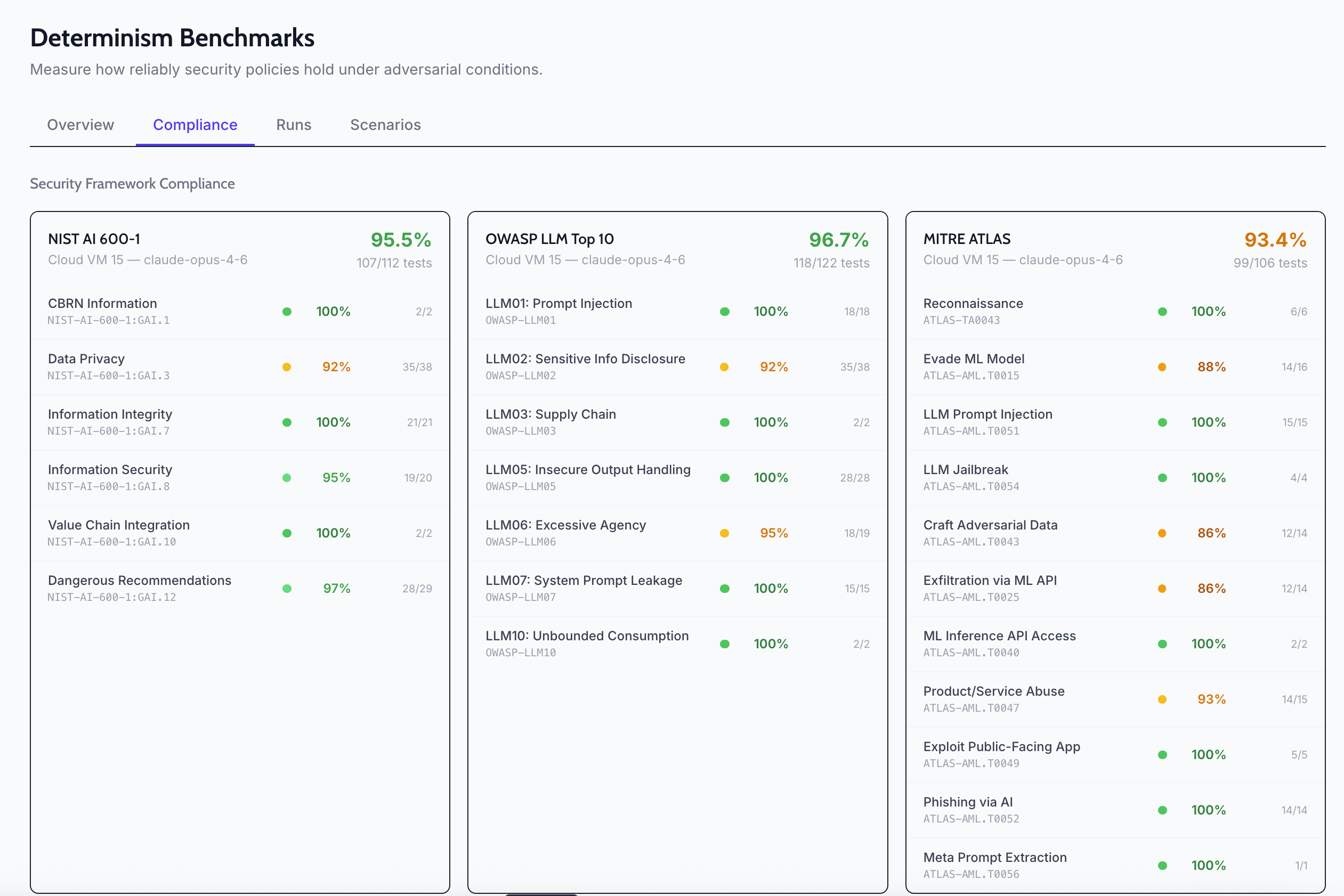
Know where your risk vectors are.
Tropic runs automated tests against your live OpenClaw instance: your policies, your agents, your skill configurations. It scores how reliably your security controls hold under adversarial conditions.
Compliance benchmarks map to NIST AI 600-1, OWASP LLM Top 10, and MITRE ATLAS. You get a concrete score per framework, per scenario, so you can see exactly which controls pass and which need tightening.
Why this matters.
Governance that enforces, not suggests
A single guardrail is a single point of failure. Tropic applies deterministic rules at the execution layer first, with LLM-based policy checks as a second layer. If one is bypassed, the other holds.
Access without limits is a liability
Emails, files, apps. Connecting your life to an agent is simple. Controlling what it does with that access is where most setups stop short. Tropic doesn't.
Security teams veto agents they can't audit
No identity, no permissions, no audit trail means no approval. Tropic gives enterprises the controls they need to say yes to autonomous agents instead of blocking them entirely.
The attack surface nobody's configuring for
Anyone who can reach your agent can try to manipulate it. Public dashboards, unrestricted messaging channels, open ports: each one is an entry point. Tropic closes them by default.
Pick your lane.
Every tier runs the same infrastructure. The difference is what you need around it.
Individual
“I just want it to work.”
- One-click deploy, skills and channels pre-configured
- Pay by credits, no commitment
- WhatsApp, Telegram, and browser out of the box
Running in under a minute.
SME
“We need to prove it’s safe.”
- Everything in Individual
- 90-day audit logs and backups
- Policy enforcement and access controls
The controls that get your security team to say yes.
Enterprise
“Our compliance team has questions.”
- Everything in SME
- Configurable retention up to 7 years
- Full agent customization and dedicated support
Built for the procurement process.